Some time ago I told a friend of mine, that I can easily beat his score in Jet Man the Facebook game, by using the well known technique of cheating.
The guy said he does not believe me, because if I could do so, then other people could do so and then there should have been many better high scores on the world wide table.
Little did he know that I'm a well trained Ninja (Or pirate, I have this identity crises right now).
I was sure it is possible and very easy to achieve, though I hadn't done anything like it, just yet.
I was very enthusiastic about it, and about a year later I started working on it. By that time I had found out that there are many people who cheat on Facebook games, so I thought that now I have to prove my superior mind.
From small research on Google, I found that the subject is more common than what I thought at first. The potential of the matter can be described in the ad found on one of the top google results:

Quickly I discovered that all of these games are written in Flash with some help of Facebook lib or so.
I went through about 5 different ways of cheating before I found the one that fits, and I'm going to describe the entire learning process I went through for other people to learn from my mistakes and maybe give me some new techniques and ideas, because I'm really out of new ones by now.
My first target was How Big Is Your Brain, which would help me prove the fact that mine is the biggest.
 Without further ado, my first attemptMemory scanning
Without further ado, my first attemptMemory scanning. As old time cheats I thought this must be the easiest and the most nostalgic way to overcome the problem.
The concept is simple, just do as following:
- Accumulate some points, search the number in the FireFox process memory. You would probably find more then one instances of the value.
- Gain some more points.
- Search for the new value among the addresses you got from the last step.
- Repeat the process until you are left with one address containing the value of your current score.
- Set the value to a big big number.
- Enjoy the results.
- Eat some pancakes, which is what every ninja do after a long day of games hacking.
One can use program like "Cheat Engine 5.4" which could be freely downloaded from
http://www.cheatengine.org/ or a python win32 debugging module.

This method fails miserably due the fact that the Flash engine saves all values in memory encoded in some way.
Google suggested that the encoding method used to be the value multiplied by eight. The encoding has changed since, and no one has yet to reveal and publish what it is (you laze ninjas).
Beside that, all strings are encrypted, no one yet to publish how (You laze pirates).
I started reverse engineering the engine, but lacked the time to complete the task (laze me).
If anyone is interested on hearing more about that, just contact me by email or so.
Method number two, using r4zcheatWhile researching the solution for the last problem, I stumbled upon an application called r4zcheat.

This neat tool, allows you to load a Flash applet and explore all the variables, their names and values and change whatever you like at real time. Isn't that awesome?!
The only problem with that is the fact that it loads the SWF file outside the browser environment, while all the Facebook games requires the browser to handle everything in communicating with Facebook.
I was not to give up just yet!
First I've asked the guy who wrote the r4zcheat to send me the source code,
but till the time of writing these words, I yet to get any answer from him. For my good luck, the guy happened to be a true hard core pirate, so after I dulled him to death he was glad to send it to me.
Reading the code, I found out that it's only taking advantage of the well documented Flash API, mainly with the function GetVariable, which is called from the ShockwaveFlash object (Some kind of all in one object that is used for all the control over the Flash engine instance). The flash application does not work inside a browser because it needs to create the Flash instance to have a reference to it and to invoke its' functions. I have tried for a little while to hook the iExplorer process, and look for the Flash instance address in memory using some pattern searching, then call these functions from an injected thread, but it took me too much time, so I decided to try another approach.
Btw, I used iExplorer and not Firefox on this attempt because there are some differences on the use of Flash between the browsers, it seems like iExplorer is using the FlashXX.ocx file while Firefox is using NPSWF32.dll. I am not so sure what is the big difference, and why there are two kinds of ways to use the embedded flash engine.
And that would bring me to the 3rd attemptFooling around with
pseudo random numbers generator.
Well I thought that If I'll just patch the flash random function to always return the same numbers, I would always get the same questions in the game, right?
This would allow me to just remember the answers to get a very nice high score (but still in the reasonable range), after all "practice makes perfect".
So back to disassembling the Flash engine. Without getting too much into boring details on how disassembling is done, I would say that I needed to find the code that is relevant to the random function, within the entire binary file.
First I dived into documentations reading about the Flash programming language which is called Action Script (the phase I like to call RTFM).
I found out that there are many versions for the language each supports a new set of opcodes, while fully backward compatible with the old ones.
By disassembling I easily found the main processing loop that reads the next instruction and execute it. The function, of course, is mostly made of a huge "Switch" like code that operate on every different opcode (I found that there are many ways to improve the code for Flash to make it run faster, but that's a different story).
I've investigated the function that handles the RANDOM opcode (0x30) to find out exactly were does it spit out the new magic figure.
Luckily I found an inner function that handles all the random functionality. This function was not aware of anything like the Flash stack or so, but just returned a value using the EAX register.
I've encoded a small patch in pure assembly (Arrr) to read the values from file, instead of using the random function.
Then I made a backup of the NPSWF32.dll file and applied the patch to it.
I'm not so sure about what have I done wrong on this attempt, I'm just sure it did not worked as I expected.
It appears that
Playfish (The company which made the "How Big Is Your Brain" game) has implemented their own random function in Action Script that uses the time as seed and some extra stuff.
I tried to make some workarounds for this, but I failed.
What would bring me straight to my 4th attemptSlowing everything down. It seems like that all the questions in the game are very easy, it's just the time limit that makes it hard, so I've decided to try to fix this problem once and for all.
I thought about it for a while, and realized that the Flash engine must use the Windows APIs to read the local machine time to implement timers (Actually there is another way using the RDTSC opcode to read the timer, but I had some hope that they don't do that because that would have required a solution in the form of a driver, which is a great pain in the ass).
The general principle behind this method is to hook the Windows API functions.
This task is very easily done using the the Microsoft Detour library (
http://research.microsoft.com/en-us/projects/detours/).
The functions we would like to hook are:
There are more APIs made up for this purpose, but I've checked the NPSWF32.dll's import table, to make sure they are not in use.
Hooking those functions is something that takes some programming time, lucky for me at this point of the project my girlfriend dumped me, which left me much more time to work on a solution.
(though it probably wasn't the best idea to ask her to proof this article...)For a better understanding of the detour library, I would recommend the help file that comes with it, and many other tutorials living out there on the net, waiting for someone to read them.
I just hooked the SetTimer to set the user input to be twice the real input.
For the GetSystemTime, GetTickCount and timeGetTime APIs I've saved the first read.
Calculated the delta from each new call to the first one.
Set the result to be the first value plus delta / 2.
This approach has got me some good results, the game was about four times slower, and I was able to get myself a very good high score.
Only until I got to the end of the game to see a message that my score was not accepted for some reason.
Bummer server timeout or something.
I guess I could have sniffed all the packets sent from my game to the server and replay those in the right times, and hope they do not conceal any time stamps.
But I found this solution to be very dull, so I moved to the next attempt.
BTW, this approach has slowed FireFox down as well, creating some very kewl effects on some websites.
Number five, and final, disassemling Action ScriptThis solution is going through the following steps:
- Get the SWF file of the game.
- Learning Active Script assembly.
- Finding a good flash disassembler.
- Making a real time patches to the game.
The first part was easy, I used CacheViewer FireFox plug-in to get the SWF file.
But, 2nd part was not as easy as it might sound. It took me a while to find a good PDF file on the subject. The only thing I was able to find was the "Action Script 2 Virtual Machine overview" PDF file (
http://www.adobe.com/devnet/actionscript/articles/avm2overview.pdf), which was quite good, but the game was using mostly Action Script 3 opcodes.
The second best thing I found was the source code of Flasm, which is an open source Flash files disassembler (
http://www.nowrap.de/flasm.html). However the Flasm is currently missing some parts as well. So, currently I settled for these , but I'm still looking for better papers on the subject, so if anyone of you pirates out there got anything better, please, do share.
Finally I've stumbled upon the commercial
Sothink SWF Decompiler program that had a free trail version, which happened to be very good.

The program had a decompiler option that gave out a very readable Action Script code. Thanks to the great extra feature of ASM view, it was very easy to locate the right point for patching.
By this method I was able to patch any code of the program but not the values nor the defaults of anything.
Further problems with this methods are:
- I can't insert code I can only patch ASM with equal amount of bytes.
- I should be very careful not to fuck up the stack.
- I had to either find a way to make FireFox load my patched SWF file or patch at run time by searching the bytes I want to patch with some memory trainer such as Cheat Engine.
- If I choose to patch at run-time, I had to do it when the code is already loaded, but not yet executed, or it would get optimized and harder to find in memory.
- Programming in Action Script assembly is hard, though, lots of fun.
To conclude, I would say that only my 5th attempt went by with good results, although, I do believe that with a little bit of an extra effort I could have make all the other attempts work as well.
I found out that many people are developing automated scripts to play the games for them, using many
OCRs and other kinds of methods, this is a very vast and interesting technique that I might write about in a future post, because now I have lots to say on the subject, and little time to do so.
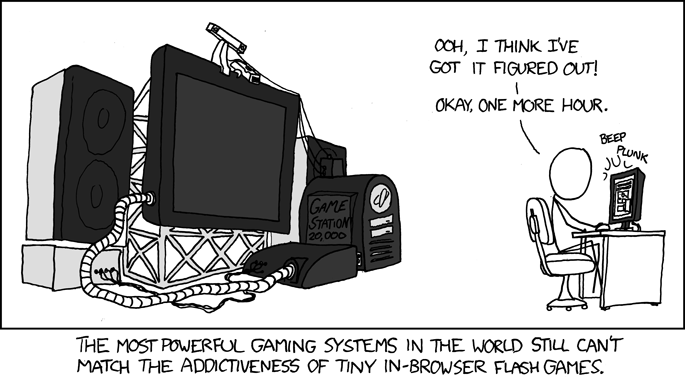
One might ask why Flash games and not something more interesting such as World Of Warcraft, and my answer would be using a picture from the outstanding web-comic
XKCD:
That's it for now. Hope you enjoyed reading this post, and got a bit of inspiration on developing ninja skills.
And remember, it's only cheating if you get caught (
Al Bundy).
Cheers,
Assaf.
Many thanks to Omer Enbar and Avital Zipori for reviewing and proofing my English.